What can you do with a phone number that used to belong to someone else? More than you think! Our security researcher Linus Särud takes a closer look at the risks posed by recycled phone numbers.
Yesterday
A long time ago – at least it feels that way, but it’s probably closer in time than you think – a @ hotmail.com address was deleted if not logged in to in a given timeframe. Once deleted, anyone could start using the address by simply signing up for a new account.
Let us imagine a scenario where you decide to switch from Hotmail to Gmail. You sign up for a Gmail account and need to provide a backup email. If you forget your password, you can use your backup email to reset it. Sounds good! You enter your Hotmail address as the backup email.
You continue using Gmail and don’t log in to your Hotmail account anymore. Fast forward to six months after you first created your Google email address. A bored teenager makes the connection between your old Hotmail account and the new Gmail account. As your Hotmail address has now expired, the teenager can sign up for a new account using that address. This allows them to reset your Gmail account as the password reset link is sent to to the new email that is under their control.
Today
In hindsight, the security problem here is obvious. While it is still possible to carry out this kind of attack under certain circumstances, most services have implemented protections and policy changes against it. The standard is no longer to recycle email addresses.
However, recycling is still a hot topic and SMS has taken email’s place.
When signing up for a new service, you still need an email address to create an account (there are exceptions!). However, it has become increasingly common for websites to allow you to add a phone number that can be used for password reset as well. In addition to password reset, your phone number can sometimes also be used for two-factor authentication.
Different telecom providers seem to have different policies in place, and this probably also varies greatly between countries. The providers we talked to say numbers are quarantined for three months after they are no longer used. After that time period, anyone is free to register and use the number again. This is the old email issue once again; same problem, different protocol.
Potential attacks
Looking at different operators, there seem to be two different attack methods that are realistic to work with.
At scale – Enumerate available numbers
When you get a new phone number you are usually free to choose between a few different options. This seems like the common case in both the US and Europe. If none of the suggestions are interesting, it is possible to re-generate a few new ones without having to redo the previous steps.
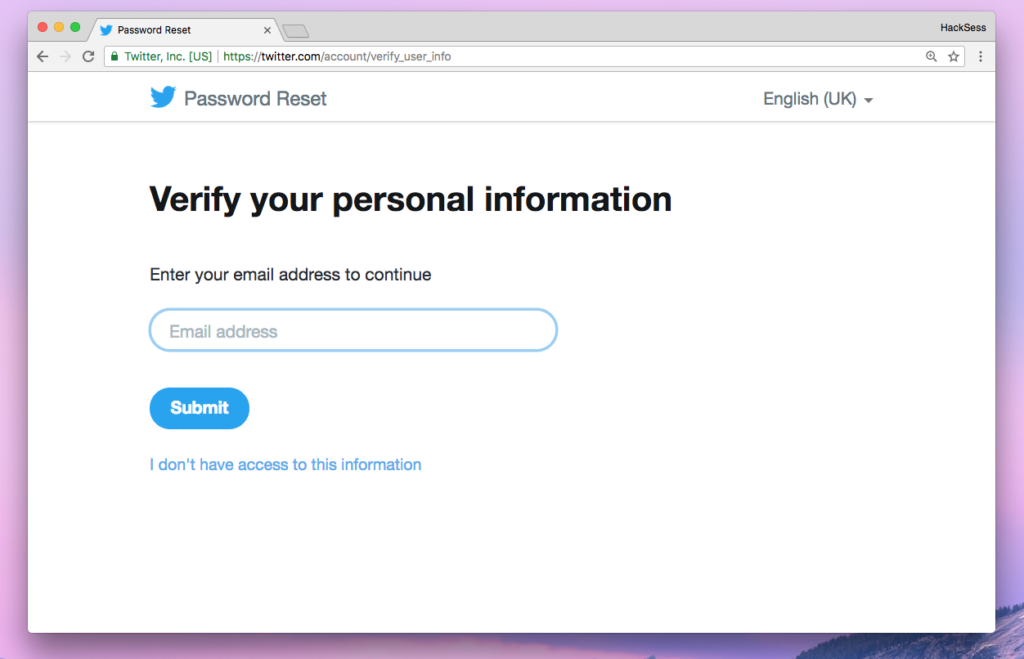
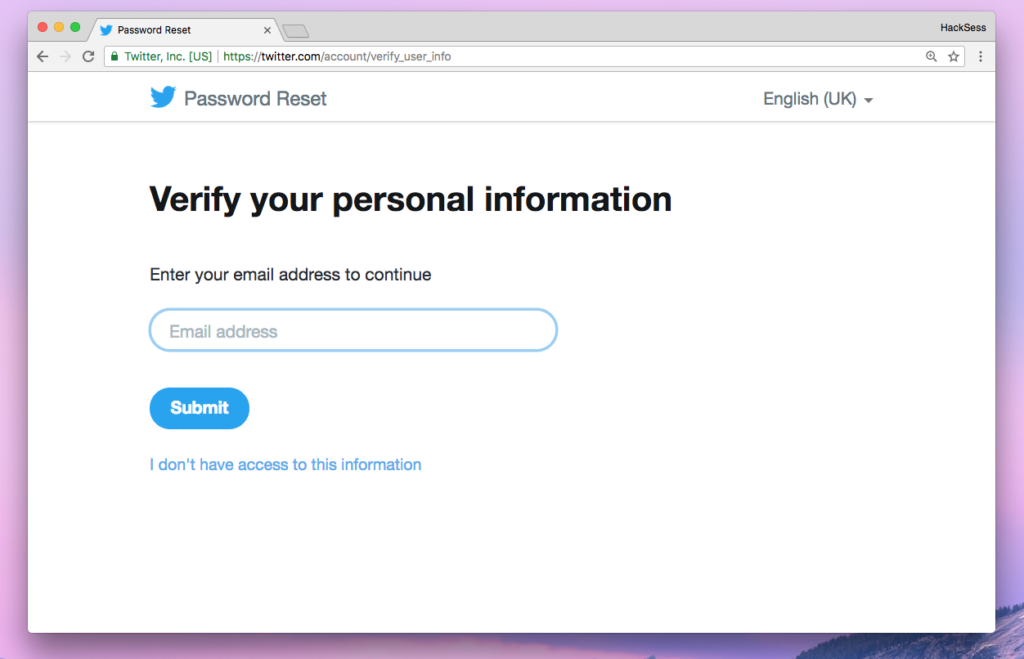
For many of the tested websites it is also possible to see if a phone number is being used or not. Here is an example screenshot from resetting a Twitter password with a registered phone number vs. one that is not registered. You would have to know the email address, but that can often be done by comparing data breaches or just using Google.

Here is how it looks on Facebook. In this case, there is no need to know the email address.


It might also be interesting to look up which account is tied to the number, if the platform allows that. That way we can take action on whether it is interesting to carry on or whether we should skip that number.
Combining all of the above, it would be possible to carry out an attack like this:
- Fetch five numbers
- If one is registered on the target platform
-
- Buy that number
- If not
- Repeat from 1
- Reset the password
Targeted – Contact support
After contacting the support of multiple telecom providers, most seem to be willing to give you a specific number, assuming it is free and not placed in quarantine. How the attack goes from there should be obvious.
Some telecom providers provide a web interface for this, while others need to be contacted before recycling a number. When we tested this approach, we got no follow-up questions as to why we wanted a specific number.
Tomorrow
It seems unlikely this problem will go away anytime soon. While the way we recycle phone numbers worldwide will probably stay the same, the way we use them could change. Either way, this most likely not going to happen in the near future.
Websites that offer password reset as a feature need to remind the user to review their settings and make sure the phone number still belongs to them. There might not be any need for this if SMS is also used for 2FA as that itself is proof the number is still active, but if the phone number is set up as 2FA backup or just used for reset, this becomes really important.
A solution for the “at scale” example is to display something like “if this number is registered, we have sent a text to it”. This is a lot less convenient for legitimate users so it boils down to a compromise between security and convenience.
What matters most for a user is remembering what accounts you have signed up for and making sure you are using your current phone number. Not entering the phone number when it is optional could be one solution, but phone numbers are sometimes also used to improve security. Even if you are not always using 2FA, some services can block an account after suspicious activity (failed logins and so on) and require proven access to the phone number to unlock. Once again, this is a question of compromise between security and convenience.
So if you have changed your phone number recently, are you really sure your old number is not used for any service? In the days of GDPR, surely everyone has gotten emails from websites they had totally forgotten about being registered at? The risk seems quite high that one or more of those supported password reset over phone number.
The idea for this article comes from a real-life case of someone’s account being taken over this way, so abuse of recycled numbers does actually happen. However, if that was targeted, done on scale, or just someone playing around with their new phone number is unclear.